Why WiFi Encryption?
In this day and age, it seems most of us have at least one WiFi Access Point in our home.
A WiFi Access Point (AP) is a device that allows wireless devices to connect to a wired network using Wi-Fi, or related standards. The AP usually is part of a router or modem. This “wired” network is typically the network used to connect to the Internet.
Since such an access point can have a range of about 300 meters (100 feet), this practically means that your neighbor(s) might be able to pick up the signal, or even worse: passing people (see also: Wardriving and PiggyBacking).
If your WiFi encryption is not enabled, then individuals like your neighbor or simply a passing person, might be able to use your Internet.
A few point to that:
- Such freeloaders will take away bandwidth from you and potentially slow down your Internet,
- These people might access, steal and/or destroy data on your computer(s),
- These individuals might use your connection for illegal downloads or other illegal activities.
Reducing your speed is one issue, but doing illegal things or accessing your private data through your WiFi is another.
As if stealing, copying or destroying your data isn’t bad enough, doing illegal things thorugh your WiFi comes with even worse problems. Crime investigators will see YOU as the person that committed the crime, with you having pretty much no evidence to who actually did it or prove your innocence. If things get really bad, so called Copyright Trolls (lawyers that intimidate and threaten you because they assume you’re the one downloading movies or music illegally) will try to make your life hell until you pay the ransom or find yourself in court.
The legality of accessing a WiFi without explicit permission, is different per country, and seems frequently changing. See also this Wiki Article on the legality of PiggyBacking.
From an ethical stand point, I’d say that accessing somebody’s WiFi without their permission is like breaking into their house. It’s simply wrong and should not be tolerated.
From a WiFi-owner perspective I do think that a certain level of responsibility is required as well. Like with your house, make sure you lock the door – even though it’s sad that this is needed, as some people seem to have no scruples or understanding of what is theirs and what is not theirs.
The latter is where WiFi encryption comes in to play as a analogy to the look on your doors.
WiFi Security through Encryption?
Most modern routers and/or modems, that function as a WiFi access point, offer some kind of encryption for WiFi.
The used standards however are puzzling at best. Below we will highlight the standards WEP, WPA and WPA2.

WiFi Alliance Logo
Since the late 90’s, WiFi encryption standards have gone through quite a lot of changes, and for good reasons.
WEP (Wired Equivalent Privacy)
WEP is one of the oldest and most widely used WiFi encryption algorithms. This doesn’t mean it’s the best choice, but due to backwards compatibility, equipment that did not get updated to the latest standards, and ignorance or laziness, are still too often being used.
Initially this standard, due to US government limitations on export of algorithms, was using only a 64 bit key, which appeared relatively easy to crack. After lifting these export limitations, 128-bit encryption appeared, but even though 256-bit encryption exists, 128-bit remained the most commonly used.
Despite WiFi encryption, some serious flaws make it very easy to exploit and crack WEP. A nice list of publicly available tools even do this automated for you. Therefor the WiFi alliance retired the WEP standard in 2004.
WEP is NOT RECOMMENDED!
If your equipment does not offer the newer standards, then I highly recommend either upgrading the firmware so it does support newer standards, or simply replacing the equipment with equipment that does support the newer standards. It seems though that old WEP only equipment cannot be upgraded with software to WPA/WP2, so a new router or modem might be needed.
WPA (WiFi Protected Access)
In 2003, a new standard was introduced called WPA, as an answer to the failing WEP WiFi encryption standard.
The most common configuration is WPA-PSK (Pre Shared Key) where the key is 256-bit, a significant improvement over the earlier 64- and 128-bit keys seen in WEP.
Another improvement, is the use of TKIP (Temporal Key Integrity Protocol) which uses a per-packet key system to verify the integrity of a packet. It is said that TKIP allows the use of hardware formerly used for WEP.
Later TKIP has been replaced by AES (Advanced Encryption Standard), offering even better protection but would require specific hardware (reference: The Difference between TKIP and AES).
For us mere mortals: AES is the recommended way to go.
WPA however isn’t perfect either and, even though a little harder to do, still vulnerable to hacking. Unlike WEP, where the algorithm is being attacked, WPA attacks focus on the WPS (WiFi Protected Setup) function of a router, often recognizable as a “setup” button on your router or modem.
WPA-AES is only to be used when WPA2 is not available.
WPA2 (WiFi Protected Access 2)
As of 2006, WPA has been replaced by WPA2, with the main difference being the mandatory use of AES and the introduction of CCMP (Counter Mode Cipher Block Chaining Message Authentication Code Protocol) as a replacement for TKIP.
Note : TKIP is still preserved in WPA2 WiFi Encryption as a fall back, for devices that only support WPA.
WPA2 is currently the recommended option.
Be aware though that even WPA2 is vulnerable, but at the time of this writing, a lot of effort needs to be done – unless one is already connected to the encrypted WiFi … but otherwise this is considered the safest way to protect your WiFi.
WPA Personal versus WPA Enterprise WiFi Encryption
When exploring the settings of your router or modem, you might run into “Personal” and “Enterprise” WiFi encryption variants. A little confusing and yes I had to Google that one myself as well. See also: WPA Personal vs Enterprise at TP-Link.
The “Personal” version is definitely intended for home use, where no additional setup is needed.
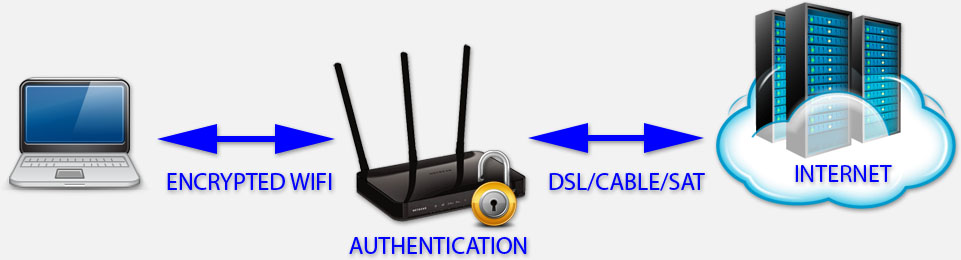
WiFi Encryption – Personal – Router handles authentication
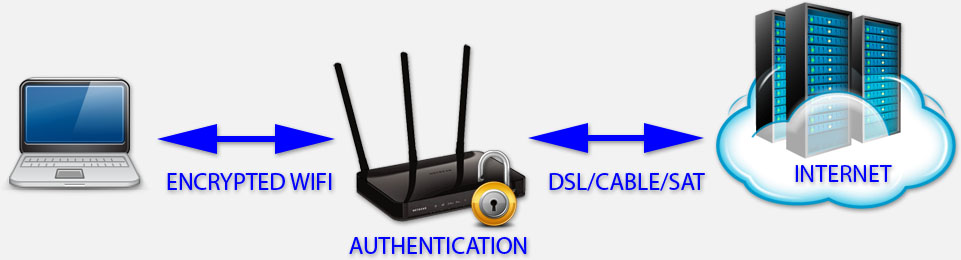
The “Enterprise” version however adds additional security by using a so called Radius server, which handles authentication. This is typically a more advanced setup and commonly used in enterprise (business) applications of WiFi. If you have such a Radius server available at home (a QNAP NAS has this option), then of course you can use this method as well, although it might make things unnecessary complicated.

WiFi Encryption – Enterprise – Radius Server handles authentication
Ranking of WiFi Encryption
Below a short list, in order of preference, which methods to use:
- WPA2 (includes the use of AES)
- WPA + AES
- WPA + TKIP/AES (TKIP is used as a fallback when AES is not available)
- WPA + TKIP
- WEP
- Encryption disabled / No Encryption
Sense of security …
Some methods seem to give a false sense of security …
Rule of thumb for good protection …
The most important part of good protection is:
– Good Encryption Algorithm (WPA2)
– Strong (long) Password
What may help (but not a guarantee):
– Mac Address Filtering
– Time Schedule WiFi availability
What will probably not help:
– Disable DHCP
– Hide SSID
– Physical location far enough from the road
Strong Password and Encryption Algorithm …
The bottom line for good security is good WiFi encryption, which builds on using the proper WiFi Encryption standard (WPA2) and a strong password. Keep in mind that WEP (the oldest standard) encrypts, but is considered UNSAFE.
A strong password is a must – don’t use easy to guess phrases and make sure you mix in capital characters, numbers and/or special characters. Also make sure the password is LONG. Most routers or modems allow up to 63 characters, … so use them. The longer the password, the harder to crack. You could even enter a simple sentence if you’d like. Make sure you save the password in a safe place though …
Maybe not a good habit, but it might be practical: write down the (long) password on a Post-It and stick it under your router or modem. Unless you router/modem is standing in a public place of course.
Hiding the SSID can make things worse …
The SSID, or “name” of your WiFi, can be hidden on most routers or modems. You’d think that this would make things more secure, but it seems that this method comes with a downside. Your computer keeps “asking” for this SSID, to see if it’s around, and with simple tools this SSID can be picked up quite easily. This is seen mostly with Windows computers as they are notoriously known for this. I honestly do not know if this problem occurs with Linux or MacOS X and other systems.
Does Disabling DHCP help …?
This one is frequently debated … does it help, or does it not help,…
Some say that disabling DHCP makes a network unmanageable, and with some trial and error one could set an IP address manually to gain access to your network.
From the other side, if you have a fixed and very limited number of devices, DHPC might throw up a tiny hurdle slowing hackers down. And connecting seems a little faster and machines persistently have the same IP address (which can be handled with DHCP in the router as well).
In the end: it’s up to you to decide if the little hurdle is really worth the hassle of managing IP addresses manually. For the average user I’d recommend leaving DHCP on and possibly reserve IP-Addresses for certain machines (a setting offered in most routers, based on MAC addresses).
MAC address filtering can add some more security …
Filtering can help, but it’s not the magic trick that guarantees that other will not enter your network.
Every NIC (Network Interface Controller) has a unique ID, knowns as MAC Address (Media Access Control Address). Most routers allow you to enter the MAC addresses of the equipment that is allowed to connect.
People with the right tools however can figure out what the MAC address is of your computer and can relatively easy change the MAC address of their computer’s NIC to that MAC address and thus gain access to the network.
It is more of a hassle though to break in … and most certainly not a bad thing to add … but it guarantees nothing.
I’m too far away from the road, so I’ll be safe …
Well, from personal experience: you’re not.
My driveway is about 900 meters (3000 feet) from the road, yet people manage to get into my network by simply driving to my house when I’m not home. So this assumption is not reliable, specially when you’re not home.
Time Schedule when WiFi is available
This method, even though not 100% watertight, will most certainly help if your router allows you to disable WiFi at given times.
For example:
I work from 8 AM to 5 PM and in that time frame nobody is home, and at night when I’m pretty sure I’m sleeping from 2 AM to 7AM. During those times I have no real view on who’s near my house anyway and I’m not using it, so why not disable it.
A possible downside, with the current trend to increased remotely accessible home automation, themostats and surveillance camera’s, is that this might not be practical – so that’s something to keep in mind.




Comments
There are 10 comments. You can read them below.
You can post your own comments by using the form below, or reply to existing comments by using the "Reply" button.
Thanks for this post Hans!
Perfect timing – Just what I needed for an organized explanation to my nephew! :-)
John
Thanks John!
Great to hear that this article was helpful for you!
hans
Your writing style reminds me of mine, which I like! And it seems you love similar geeky stuff as me – haven’t tried XBMC (I just can’t get used to KODI as a name) on an Amazon fire TV – I gave up on XBMC in the end but after many gateful years and ended up going for Plex – possibly because my Raspberry Pi was a bit slow for a network connected MYSQL database and I just got lazy, it would be great if Plex ran on the QNAP well, but I don’t think even the new models will do well until it can take advantage of the new acceleration – maybe you’ve tried it? How are you finding the Raspberry Pi 2? BTW, the ‘your website section of this form doesn’t like putting in a dash (-) which is valid as I have one in my domain name.
Q
marshalleq
Hi Marshalleq!
Thank you for the nice compliment. I’ll take a note of the dash in a URL issue, I had not noticed that yet. I’m midst moving from the USA to the Netherlands, so it will have to go on the “ToDo” list for now .
.
Sorry to hear you gave up on XBMC/Kodi. I have done some trials with Plex but I’ve found that streaming just doesn’t do it for me.
The original A and B models Raspberry Pi are indeed somewhat slow. The new Raspberry Pi 2 however performs pretty good.
QNAP does support Plex, but as a streaming service I transcodes videos (if I’m understanding Plex right), for which certain QNAP models might not be adequate. I haven’t tried though. A friend of mine worked with Plex on a QNAP 859 for a bit, but I have to say that, even though it worked, it would annoy the heck out of me. Just minor lag and such.
As for the new Raspberry Pi 2: I’m pretty impressed by it. It is very responsive, works very smooth. I’ve been running it with OpenElec, but I have yet to try the MySQL connection – since everything is in a large container on a boat to the Netherlands.
hans
Well, XBMC just kind of got ‘harder’ to maintain, with Plex I can set it and forget it – and I can use Apple TV with it which is a nice device for the price. I used OpenElec for quite a while too – fantastic little distribution actually – ended up using RaspBMC on my Pi though, it just seemed more optimised at the time. Yeah QNAP supports plex, but it doesn’t transcode HD content really, even on the new processors that are accelerated, there is no plugin between that and the Plex Media Server so it can’t take advantage of it. Never been to the Netherlands, my friend lived there for a year (I’m from NZ) but I hear it’s an amazing place – best of luck on your move, will bookmark your site and keep an eye on it – looks like we’re doing similar things!
Q
marshalleq
Hi again Marshalleq!
It seems we have similar interests – I think that’s pretty cool!
 .
.
I have never been to NZ, but I should probably put it on my “ToDo” list
Having a large MySQL database can be a bit of work for the Amazon Fire TV and/or Raspberry Pi. I’ve noticed that my Amazon Fire TV Stick takes a little bit of time to get started, specially the first time when it connects to the database.
Once it’s started however, it work pretty smooth – more testing is needed on my end though, as I had very little time to test while I was in the USA to pack my stuff.
If Plex works well for you: by all means, keep using it. I think a good (wired) network connection is a requirement though. WiFi can work, but the few instances I have seen Plex at work with WiFi made me abandon Plex altogether. Of course, later I learned that WiFi in general seems to disappoint when using it for media – specially when one has plenty WiFi enabled devices connected.
Kodi/XBMC however does seem less sensitive to that due to the nature of how data is transmitted.
Maybe I’ll play with Plex again in the future (based on your experiences).
hans
Yeah – Cable is definately better, but I’m in an apartment now and have little choice. I ended up getting two Asus AC-68U routers and making a bridge, what made a world of difference was getting a set of super power supply antenna’s to boos the signal, $22 all up for 6 antenna’s wasn’t too bad. I have a NAS with some media on it that’s plugged into the router, the Plex Server runs on my Mac which is connected straight to the ASUS bridge by cable and the apple TV is connected only via WiFi. I seldom have any problems so it can work, but if I had a choice I’d definately switch back to wired. The bridge connects at about 800Mbpps compared to the 1.3 it’s supposed to have so in reality I’m probably only getting about 500 in terms of true performance. WIth that I can play a file that’s 20GB in size no problem. The Mac transcodes it from the NAS and streams it back to the ATV. It’ll direct place to tablets and laptops without any transcoding too – it works quite well. Mac just isn’t great at mapping network drives so I do have to log in all the time – the bonus is that Mac’s don’t get slow or need reboots as often as windows does. Plex of course runs on linux too – I assume that has a headless mode similar to the Mac one. All good!
marshalleq
Haha, I did something similar: I bought a Netgear AC router and replaced the antenna’s as well.
Bridging connections however, I have not tried yet with WiFi. I do use it for my QNAP though (2x 1Gbps). How did you do that?
hans
It’s just a wireless bridge. So the Routers are essentially connecting their internal ethernet ports together via the wireless link. One of the routers doubles as an access point and the other is a straight bridge. You can make the second unit a repeater as well. The advantage is that the connection for any client on the other side of the bridge is much faster and more stable as the routers have better send / receive strength / quality. In this way I’ve got a lot closer to the 1Gbps cable speed over wifi – I can’t get anything like this without the bridge. It’s also much more stable considering I’m running a server on it – I can’t say it’s 100% perfect but it’s pretty darn good. You just enabled it in the wireless settings on most routers. One catch is broadcast traffic i.e. apple protocols don’t like the bridge and you have to turn this on as a special setting – if you need it (common problem).
marshalleq
Interesting – I had not heard of that before.
So for this one would need 2 routers … hmm I’ll have to investigate that a little more, just to see if I can use it some how.
hans